Is there a TailsOS template available for QubesOS?
Tails is an “amnesic” OS, everything is lost when you shut it down. It makes no sense to have a template based on it. The only proper way to use it is to live boot it from a USB key. Running it inside Qubes will leave traces that it was used, which defeats its purpose.
You can use Whonix with a disposable VM instead: Qubes Disposables
TailsOS actually does have the option to create a persistent volume. The tricky part is knowing how to create the TailsOS installation on a USB stick with persistent storage, and then copy it to a Qubes VM
using HVM. That is documented in the following article:
However, there are still some issues with it, the mouse doesn’t always work inside the VM, and also
the Tor network connection hasn’t worked yet.
It would be nice if more users tried this setup so that bugs can be documented and fixed.
The other part of the discussion is…what af(anti-forensic) features does TailsOS have that QubesOS doesn’t?
done it and it looks and feels like the one (TailsOS) on my stick. But network isn’t reachable.
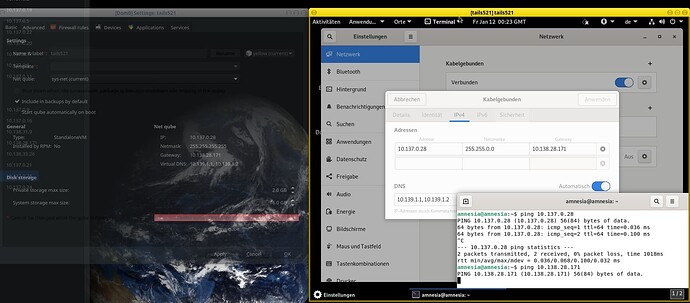
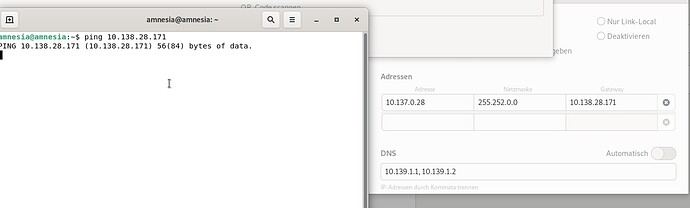
I manually set the network settings as it should be in Tails network means IP=Tails Qube // Subnet=255.255.255.0 // Gateway=netVM
Nothing! It can ping itself, but ping to gatewayIP 100% loss
Tried on my two machines (NitroPC & Lenovo P50)
It’s not designed for that. If you want to create a TAILS template, I’d say why not? It can certainly be an interesting expercise and have some uses, for example development amd documentation:
But if you want the features that TAILS was designed for… I’d use TAILS the way it’s intended to be used. It was designed with a given use in mind, so changing that context without changing the design seems like a mistake to me. YMMV
what it means “givem” use?
Which VM should be used for network connection? sys-firewall, sys-net, or sys-whonix?
You definitely need to manually configure the network settings, but it won’t connect to anything without
a Tor network connection. This might even require the use of a bridge.
A template is not ideal because it could leave metadata right?
It would be best to use the persistent volume function within the TailsOS VM itself, although it’s
not clear which filesystem type is used and whether or not it is encrypted or uses a hidden partition, etc.
You need to choose sys-net for networking and then enter the network settings manually inside the TailsOS
VM. The correct settings are under the TailsOS HVM Settings → “Net Qube” section
IP, Netmask, Gateway, Virtual DNS (these all need to be entered into the TailsOS VM)
Once the regular network connection is made, you need to request an bridge from the Tor Bridges website
and then manually input the bridge into the textbox for bridges.
It’s litterally written in the TAILS documentation:
Can I install Tails permanently onto my hard disk?
This is not possible using the recommended installation methods. Tails is designed to be a live system running from a removable media: USB stick or DVD.
This is a conscious decision as this mode of operation is better for what we want to provide to Tails users: amnesia, the fact that Tails leaves no traces on the computer after a session is closed. (source)
still not possible for me! Changed the net settings in Tails manually as the screenshot shows, but no ping except the ping to it’s own…
PS.: and even setting the subnet to 255.255.255.255 - same result
that’s just the first step. The second step is to create the Tor network connection using a bridge.
so you mean, a connection will be possible, even there’s no ping to my sys-net qube ?
Then I have to insert the bridge into Tails manually letter for letter, cause STRG+SHIFT+C and STRG+SHIFT+V even won’t work…
PS.: Yes - even with inserting a bridge - no connection. I can’t reach the netVM. The Tails Qube is logged out from the rest of the qubes network. He see it’s own (localhost) only.
Does it say “Wired Connected” in the network settings in TailsVM?
The steps I found tricky with this were just making sure you have the correct number of dashes in the
qvm-run -p $dispVM "sudo cat /dev/sda" | sudo dd status=progress of=/dev/mapper/qubes_dom0-vm--$qubename-root
step
and also, when you boot up the VM, you need to very quickly hit the down arrow key(the instructions don’t mention this) and then tab to bring up the screen where you can then follow these steps:
- When the syslinux boot screen shows up, press tab to edit the boot parameters
- Remove the
live-media=removableparameter and press enter
Set netmask to 255.252.0.0.
yes
Found out, if you doing any mistake there - it mostly repeat with errors. Took me a while to found out my correct partition file…
For my system it never is qubes_dom0-vm--$qubename-root. It always was: qubes_dom0-vm--$qubename--root
Make sure the sys-usb template is up to date (sudo apt update && sudo apt upgrade) first.
Also, the template for sys-usb needs to be running.
it’s running, Mouse support on all other qubes and even, if I NOT use the down arrow (means using the Tails 5.21 entry as of the Troubleshooting entry instead)
Tested on two devices (Lenovo P50 & Nitro-PC)