Hello everybody,
I am trying to set up a ProxyVM on Qubes 4.2 to route traffic through a VLESS/REALITY proxy. The ultimate goal is to chain it before an AppVM (or even sys-whonix), so that all traffic from the client qube is transparently tunneled.
Here is my setup:
A StandaloneVM based on the Debian 12 template, named sys-proxy.
sys-proxy has networking set to sys-firewall and "Provides network" is enabled.
xray (latest version) is installed and the systemd service is running.
The sys-proxy …
I’m trying to set up Xray with AmneziaVPN to use then in tor.
I’ve created stanaloneVM on fedora41 xfce (sys-firewall, share network to other option is enabled, installed AmneziaVPN, connected to my config. But it doesnt work even in this qube, I can’t ping google.com or any other domains. I can ping 1.1.1.1
I guess the problem with DNS or something else? I have no idea how to resolve that. And do I need to add something into firewall settings of this vpn qube?
Post your config.
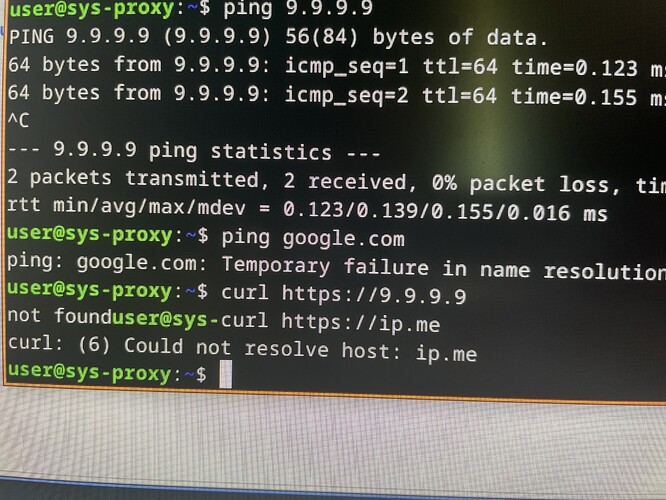
curl https://9.9.9.9 # to check if you're able to connect to IP address
curl https://ip.me # to check if domain resolution works as well
Or specify the socks directly in curl/wget/etc command for a test.
here what I have. Which config do you want me to send?
Describe all your steps in sys-proxy and its template that you did to run xray, post xray config and how do you run xray/tun2socks/etc.
I clicked “create new qube”, chose standalone qube, entered name, clicked on “launch qube setting after creation”, template is fedora-41-xfce, network connection cusotm: sys-firewall (in terms if default could change), in advanced settings clicked “provides network access to other qubes”. When it’s created settings are opened, I clicked “start qube automatically on boot”.
Then I’ve opened firefox, searched amnezia github, downloaded archieve, unpacked and installed. Then went to setting of the qube, refreshed applications and added AmneziaVPN. Then opened it and entered my server creds. I also clicked in amnezia on “open on boot” and “connect on open”.
The I’ve tried to go to some websites, none of them could open. I can’t ping any domains (“tenporary failure in name resolution”). That’s it.
Now I got it, I thought you’re using xray-core with amnezia:
Amnezia Xray-core fork
Post the output of these commands in sys-proxy:
cat /etc/resolv.conf
resolvectl
sudo nft list ruleset
You can edit the output of these commands to change your server public IP address to some random string you’ll have it there.
user@sys-proxy:~$ cat /etc/resolv.conf
nameserver 1.1.1.1
nameserver 1.0.0.1
user@sys-proxy:~$ resolvectl
bash: resolvectl: command not found
I’ve tried to change resolv.conf to 1.1.1.1 and 1.0.0.1, but it didn’t help. It was different before that.
Here’s ruleset:
table ip qubes {
set downstream {
type ipv4_addr
}
set allowed {
type ifname . ipv4_addr
}
chain prerouting {
type filter hook prerouting priority raw; policy accept;
iifgroup 2 goto antispoof
ip saddr @downstream counter packets 0 bytes 0 drop
}
chain antispoof {
iifname . ip saddr @allowed accept
counter packets 0 bytes 0 drop
}
chain postrouting {
type nat hook postrouting priority srcnat; policy accept;
oifgroup 2 accept
oif "lo" accept
masquerade
}
chain input {
type filter hook input priority filter; policy drop;
jump custom-input
ct state invalid counter packets 0 bytes 0 drop
iifgroup 2 udp dport 68 counter packets 0 bytes 0 drop
ct state established,related accept
iifgroup 2 meta l4proto icmp accept
iif "lo" accept
iifgroup 2 counter packets 0 bytes 0 reject with icmp host-prohibited
counter packets 0 bytes 0
}
chain forward {
type filter hook forward priority filter; policy accept;
jump custom-forward
ct state invalid counter packets 0 bytes 0 drop
ct state established,related accept
oifgroup 2 counter packets 0 bytes 0 drop
}
chain custom-input {
}
chain custom-forward {
}
chain dnat-dns {
type nat hook prerouting priority dstnat; policy accept;
ip daddr 10.139.1.1 udp dport 53 dnat to 1.1.1.1
ip daddr 10.139.1.1 tcp dport 53 dnat to 1.1.1.1
ip daddr 10.139.1.2 udp dport 53 dnat to 1.0.0.1
ip daddr 10.139.1.2 tcp dport 53 dnat to 1.0.0.1
}
}
table ip6 qubes {
set downstream {
type ipv6_addr
}
set allowed {
type ifname . ipv6_addr
}
chain antispoof {
iifname . ip6 saddr @allowed accept
counter packets 0 bytes 0 drop
}
chain prerouting {
type filter hook prerouting priority raw; policy accept;
iifgroup 2 goto antispoof
ip6 saddr @downstream counter packets 0 bytes 0 drop
}
chain postrouting {
type nat hook postrouting priority srcnat; policy accept;
oifgroup 2 accept
oif "lo" accept
masquerade
}
chain _icmpv6 {
meta l4proto != ipv6-icmp counter packets 0 bytes 0 reject with icmpv6 admin-prohibited
icmpv6 type { nd-router-advert, nd-redirect } counter packets 0 bytes 0 drop
accept
}
chain input {
type filter hook input priority filter; policy drop;
jump custom-input
ct state invalid counter packets 0 bytes 0 drop
ct state established,related accept
iifgroup 2 goto _icmpv6
iif "lo" accept
ip6 saddr fe80::/64 ip6 daddr fe80::/64 udp dport 546 accept
meta l4proto ipv6-icmp accept
counter packets 0 bytes 0
}
chain forward {
type filter hook forward priority filter; policy accept;
jump custom-forward
ct state invalid counter packets 0 bytes 0 drop
ct state established,related accept
oifgroup 2 counter packets 0 bytes 0 drop
}
chain custom-input {
}
chain custom-forward {
}
}
table ip qubes-firewall {
chain forward {
type filter hook forward priority filter; policy drop;
ct state established,related accept
iifname != "vif*" accept
}
chain prerouting {
type filter hook prerouting priority raw; policy accept;
}
chain postrouting {
type filter hook postrouting priority raw; policy accept;
}
}
table ip6 qubes-firewall {
chain forward {
type filter hook forward priority filter; policy drop;
ct state established,related accept
iifname != "vif*" accept
}
chain prerouting {
type filter hook prerouting priority raw; policy accept;
}
chain postrouting {
type filter hook postrouting priority raw; policy accept;
}
}
# Warning: table ip filter is managed by iptables-nft, do not touch!
table ip filter {
chain amnvpn.anchors {
counter packets 8 bytes 368 jump amnvpn.a.000.allowLoopback
counter packets 8 bytes 368 jump amnvpn.a.320.allowDNS
counter packets 8 bytes 368 jump amnvpn.a.310.blockDNS
counter packets 8 bytes 368 jump amnvpn.a.300.allowLAN
counter packets 8 bytes 368 jump amnvpn.a.290.allowDHCP
counter packets 8 bytes 368 jump amnvpn.a.200.allowVPN
counter packets 8 bytes 368 jump amnvpn.a.120.blockNets
counter packets 8 bytes 368 jump amnvpn.a.110.allowNets
counter packets 8 bytes 368 jump amnvpn.a.100.blockAll
}
chain amnvpn.a.000.allowLoopback {
}
chain amnvpn.000.allowLoopback {
oifname "lo*" counter packets 0 bytes 0 accept
}
chain amnvpn.a.320.allowDNS {
}
chain amnvpn.320.allowDNS {
}
chain amnvpn.a.310.blockDNS {
}
chain amnvpn.310.blockDNS {
udp dport 53 counter packets 0 bytes 0 reject
tcp dport 53 counter packets 0 bytes 0 reject
}
chain amnvpn.a.300.allowLAN {
}
chain amnvpn.300.allowLAN {
ip daddr 10.0.0.0/8 counter packets 0 bytes 0 accept
ip daddr 169.254.0.0/16 counter packets 0 bytes 0 accept
ip daddr 172.16.0.0/12 counter packets 0 bytes 0 accept
ip daddr 192.168.0.0/16 counter packets 0 bytes 0 accept
ip daddr 224.0.0.0/4 counter packets 0 bytes 0 accept
ip daddr 255.255.255.255 counter packets 0 bytes 0 accept
}
chain amnvpn.a.290.allowDHCP {
}
chain amnvpn.290.allowDHCP {
ip daddr 255.255.255.255 udp sport 68 udp dport 67 counter packets 0 bytes 0 accept
}
chain amnvpn.a.200.allowVPN {
}
chain amnvpn.200.allowVPN {
oifname "amn0*" counter packets 0 bytes 0 accept
oifname "tun0*" counter packets 0 bytes 0 accept
oifname "tun2*" counter packets 0 bytes 0 accept
}
chain amnvpn.a.120.blockNets {
}
chain amnvpn.120.blockNets {
}
chain amnvpn.a.110.allowNets {
}
chain amnvpn.110.allowNets {
}
chain amnvpn.a.100.blockAll {
}
chain amnvpn.100.blockAll {
counter packets 0 bytes 0 reject
}
chain OUTPUT {
type filter hook output priority filter; policy accept;
counter packets 8 bytes 368 jump amnvpn.anchors
}
}
# Warning: table ip6 filter is managed by iptables-nft, do not touch!
table ip6 filter {
chain amnvpn.anchors {
counter packets 17 bytes 1088 jump amnvpn.a.000.allowLoopback
counter packets 17 bytes 1088 jump amnvpn.a.310.blockDNS
counter packets 17 bytes 1088 jump amnvpn.a.300.allowLAN
counter packets 17 bytes 1088 jump amnvpn.a.290.allowDHCP
counter packets 17 bytes 1088 jump amnvpn.a.250.blockIPv6
counter packets 17 bytes 1088 jump amnvpn.a.200.allowVPN
counter packets 17 bytes 1088 jump amnvpn.a.100.blockAll
}
chain amnvpn.a.000.allowLoopback {
}
chain amnvpn.000.allowLoopback {
oifname "lo*" counter packets 0 bytes 0 accept
}
chain amnvpn.a.310.blockDNS {
}
chain amnvpn.310.blockDNS {
udp dport 53 counter packets 0 bytes 0 reject
tcp dport 53 counter packets 0 bytes 0 reject
}
chain amnvpn.a.300.allowLAN {
}
chain amnvpn.300.allowLAN {
ip6 daddr fc00::/7 counter packets 0 bytes 0 accept
ip6 daddr fe80::/10 counter packets 0 bytes 0 accept
ip6 daddr ff00::/8 counter packets 0 bytes 0 accept
}
chain amnvpn.a.290.allowDHCP {
}
chain amnvpn.290.allowDHCP {
ip6 daddr ff00::/8 udp sport 546 udp dport 547 counter packets 0 bytes 0 accept
}
chain amnvpn.a.250.blockIPv6 {
}
chain amnvpn.250.blockIPv6 {
oifname != "lo*" counter packets 0 bytes 0 reject
}
chain amnvpn.a.200.allowVPN {
}
chain amnvpn.200.allowVPN {
oifname "amn0*" counter packets 0 bytes 0 accept
oifname "tun0*" counter packets 0 bytes 0 accept
oifname "tun2*" counter packets 0 bytes 0 accept
}
chain amnvpn.a.100.blockAll {
}
chain amnvpn.100.blockAll {
counter packets 0 bytes 0 reject
}
chain OUTPUT {
type filter hook output priority filter; policy accept;
counter packets 17 bytes 1088 jump amnvpn.anchors
}
}
table ip raw {
chain amnvpn.anchors {
counter packets 8 bytes 368 jump amnvpn.a.100.vpnTunOnly
}
chain amnvpn.a.100.vpnTunOnly {
}
chain amnvpn.100.vpnTunOnly {
counter packets 0 bytes 0 accept
}
chain PREROUTING {
type filter hook prerouting priority raw; policy accept;
counter packets 8 bytes 368 jump amnvpn.anchors
}
}
table ip6 raw {
chain amnvpn.anchors {
counter packets 14 bytes 884 jump amnvpn.a.100.vpnTunOnly
}
chain amnvpn.a.100.vpnTunOnly {
}
chain amnvpn.100.vpnTunOnly {
counter packets 0 bytes 0 accept
}
chain PREROUTING {
type filter hook prerouting priority raw; policy accept;
counter packets 14 bytes 884 jump amnvpn.anchors
}
}
# Warning: table ip nat is managed by iptables-nft, do not touch!
table ip nat {
chain amnvpn.anchors {
counter packets 4 bytes 208 jump amnvpn.a.100.transIp
}
chain amnvpn.a.100.transIp {
}
chain amnvpn.100.transIp {
counter packets 0 bytes 0 masquerade
}
chain POSTROUTING {
type nat hook postrouting priority srcnat; policy accept;
counter packets 4 bytes 208 jump amnvpn.anchors
}
}
# Warning: table ip6 nat is managed by iptables-nft, do not touch!
table ip6 nat {
chain amnvpn.anchors {
counter packets 4 bytes 288 jump amnvpn.a.100.transIp
}
chain amnvpn.a.100.transIp {
}
chain amnvpn.100.transIp {
counter packets 0 bytes 0 XT target MASQUERADE not found
}
chain POSTROUTING {
type nat hook postrouting priority srcnat; policy accept;
counter packets 4 bytes 288 jump amnvpn.anchors
}
}
# Warning: table ip mangle is managed by iptables-nft, do not touch!
table ip mangle {
chain amnvpn.anchors {
counter packets 8 bytes 368 jump amnvpn.a.100.tagPkts
}
chain amnvpn.a.100.tagPkts {
}
chain amnvpn.100.tagPkts {
meta cgroup 1383 counter packets 0 bytes 0 meta mark set 0x3211
}
chain OUTPUT {
type route hook output priority mangle; policy accept;
counter packets 8 bytes 368 jump amnvpn.anchors
}
}
# Warning: table ip6 mangle is managed by iptables-nft, do not touch!
table ip6 mangle {
chain amnvpn.anchors {
counter packets 17 bytes 1088 jump amnvpn.a.100.tagPkts
}
chain amnvpn.a.100.tagPkts {
}
chain amnvpn.100.tagPkts {
meta cgroup 1383 counter packets 0 bytes 0 meta mark set 0x3211
}
chain OUTPUT {
type route hook output priority mangle; policy accept;
counter packets 17 bytes 1088 jump amnvpn.anchors
}
}
Check if the DNS resolution will work in the qube connected to the sys-proxy.
oohhh bruuuhh… it works. I’m not sure if it would work if I haven’t changed resolv.conf, but it works in other qubes. Thank you. Finally can connect to TOR
No idea why DNS resolution doesn’t work inside sys-proxy, it should be something specific to AmneziaVPN./rw/config/rc.local of sys-proxy):
Good news, with fedora-38 the network manager supports Wireguard out of the box!
The only thing required are extra firewall rules in the VPN qube, as explained in the community documentation about VPN .
thank you, yeah, I’ll definitely try to set up dns, Amnezia has a function with its own dns on my server where VPN is hosted, and I’ll be able to connect to this DNS if I’m connected to the VPN.
Is it good?
To set up dns, is it better to do in sys-proxy or in other qubes which are connected to it?
Yes, if you have DNS server running on your VPS, then you can use it in sys-proxy. Change 9.9.9.9 used in the link above to your VPS private IP address in VPN e.g. 10.8.1.1.
1 Like
Hey, I don’t know why, but it’s not working. It was working, but I turned the pc on today and it’s not working. There’s an issue in DNS, I’m sure in that.
So, I’m using Xray with Amnezia GUI official app. When I’m connecting to the vpn, I can’t ping any domain, ips are good. When I’m disconnected, it all works. I’ve tried to change resolv.conf to 1.1.1.1 and 1.0.0.1, but when I’m restarting this qube, it changes to default 10.139.1.1 and 10.139.1.2
When I change it to 1.1.1.1, I still can’t access any domain, but I guess it’s because the Network Manager should be reloaded. But when it reloads, I receive default values.
I’ve tested DNS in both sys-vpn (I renamed from sys-proxy) and in other qubes which uses sys-vpn.
I can’t add VPN connection through normal Network Manager as there is no Xray, and WG or OpenVPN are blocked in my country.
Follow the guide that I linked before:
Ok, do I need to write this command in sys-vpn or in dom0?
Oh, I guess I need to write it here? in /rw/config/rc.local?
I did it like this, but still doesn’t work in sys-vpn nor in other connected qubes.
What’s the output of these commands in sys-vpn?
cat /rw/config/rc.local
sudo nft list ruleset
cat /rw/config/rc.local:
#!/bin/sh
# This script will be executed at every VM startup, you can place your own
# custom commands here. This includes overriding some configuration in /etc,
# starting services etc.
#
# Executable scripts located in /rw/config/rc.local.d with the extension
# '.rc' are executed immediately before this rc.local.
# Example:
# /rw/config/rc.local.d/custom.rc
#
# Example for overriding the whole CUPS configuration:
# rm -rf /etc/cups
# ln -s /rw/config/cups /etc/cups
# systemctl --no-block restart cups
DNS=9.9.9.9
nft flush chain qubes dnat-dns
nft add rule ip qubes dnat-dns \
meta l4proto { tcp, udp } \
ip daddr {10.139.1.1,10.139.1.2} \
th dport 53
dnat to "$DNS"
echo "nameserver 9.9.9.9" > /etc/resolv.conf
sudo nft list ruleset:
table ip qubes {
set downstream {
type ipv4_addr
}
set allowed {
type ifname . ipv4_addr
}
chain prerouting {
type filter hook prerouting priority raw; policy accept;
iifgroup 2 goto antispoof
ip saddr @downstream counter packets 0 bytes 0 drop
}
chain antispoof {
iifname . ip saddr @allowed accept
counter packets 0 bytes 0 drop
}
chain postrouting {
type nat hook postrouting priority srcnat; policy accept;
oifgroup 2 accept
oif "lo" accept
masquerade
}
chain input {
type filter hook input priority filter; policy drop;
jump custom-input
ct state invalid counter packets 0 bytes 0 drop
iifgroup 2 udp dport 68 counter packets 0 bytes 0 drop
ct state established,related accept
iifgroup 2 meta l4proto icmp accept
iif "lo" accept
iifgroup 2 counter packets 0 bytes 0 reject with icmp host-prohibited
counter packets 0 bytes 0
}
chain forward {
type filter hook forward priority filter; policy accept;
jump custom-forward
ct state invalid counter packets 0 bytes 0 drop
ct state established,related accept
oifgroup 2 counter packets 0 bytes 0 drop
}
chain custom-input {
}
chain custom-forward {
}
chain dnat-dns {
type nat hook prerouting priority dstnat; policy accept;
ip daddr 10.139.1.1 udp dport 53 dnat to 10.139.1.1
ip daddr 10.139.1.1 tcp dport 53 dnat to 10.139.1.1
ip daddr 10.139.1.2 udp dport 53 dnat to 10.139.1.2
ip daddr 10.139.1.2 tcp dport 53 dnat to 10.139.1.2
}
}
table ip6 qubes {
set downstream {
type ipv6_addr
}
set allowed {
type ifname . ipv6_addr
}
chain antispoof {
iifname . ip6 saddr @allowed accept
counter packets 0 bytes 0 drop
}
chain prerouting {
type filter hook prerouting priority raw; policy accept;
iifgroup 2 goto antispoof
ip6 saddr @downstream counter packets 0 bytes 0 drop
}
chain postrouting {
type nat hook postrouting priority srcnat; policy accept;
oifgroup 2 accept
oif "lo" accept
masquerade
}
chain _icmpv6 {
meta l4proto != ipv6-icmp counter packets 0 bytes 0 reject with icmpv6 admin-prohibited
icmpv6 type { nd-router-advert, nd-redirect } counter packets 0 bytes 0 drop
accept
}
chain input {
type filter hook input priority filter; policy drop;
jump custom-input
ct state invalid counter packets 0 bytes 0 drop
ct state established,related accept
iifgroup 2 goto _icmpv6
iif "lo" accept
ip6 saddr fe80::/64 ip6 daddr fe80::/64 udp dport 546 accept
meta l4proto ipv6-icmp accept
counter packets 0 bytes 0
}
chain forward {
type filter hook forward priority filter; policy accept;
jump custom-forward
ct state invalid counter packets 0 bytes 0 drop
ct state established,related accept
oifgroup 2 counter packets 0 bytes 0 drop
}
chain custom-input {
}
chain custom-forward {
}
}
table ip qubes-firewall {
chain forward {
type filter hook forward priority filter; policy drop;
ct state established,related accept
iifname != "vif*" accept
}
chain prerouting {
type filter hook prerouting priority raw; policy accept;
iifname != "vif*" ip saddr 10.137.0.15 drop
}
chain postrouting {
type filter hook postrouting priority raw; policy accept;
oifname != "vif*" ip daddr 10.137.0.15 drop
}
}
table ip6 qubes-firewall {
chain forward {
type filter hook forward priority filter; policy drop;
ct state established,related accept
iifname != "vif*" accept
}
chain prerouting {
type filter hook prerouting priority raw; policy accept;
}
chain postrouting {
type filter hook postrouting priority raw; policy accept;
}
}
# Warning: table ip filter is managed by iptables-nft, do not touch!
table ip filter {
chain amnvpn.anchors {
counter packets 204 bytes 16232 jump amnvpn.a.000.allowLoopback
counter packets 104 bytes 6808 jump amnvpn.a.320.allowDNS
counter packets 104 bytes 6808 jump amnvpn.a.310.blockDNS
counter packets 4 bytes 184 jump amnvpn.a.300.allowLAN
counter packets 4 bytes 184 jump amnvpn.a.290.allowDHCP
counter packets 4 bytes 184 jump amnvpn.a.200.allowVPN
counter packets 4 bytes 184 jump amnvpn.a.120.blockNets
counter packets 4 bytes 184 jump amnvpn.a.110.allowNets
counter packets 4 bytes 184 jump amnvpn.a.100.blockAll
}
chain amnvpn.a.000.allowLoopback {
counter packets 200 bytes 16048 jump amnvpn.000.allowLoopback
}
chain amnvpn.000.allowLoopback {
oifname "lo*" counter packets 100 bytes 9424 accept
}
chain amnvpn.a.320.allowDNS {
counter packets 100 bytes 6624 jump amnvpn.320.allowDNS
}
chain amnvpn.320.allowDNS {
oifname "amn0*" ip daddr 1.1.1.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "amn0*" ip daddr 1.1.1.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "tun0*" ip daddr 1.1.1.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "tun0*" ip daddr 1.1.1.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "tun2*" ip daddr 1.1.1.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "tun2*" ip daddr 1.1.1.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "amn0*" ip daddr 1.0.0.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "amn0*" ip daddr 1.0.0.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "tun0*" ip daddr 1.0.0.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "tun0*" ip daddr 1.0.0.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "tun2*" ip daddr 1.0.0.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "tun2*" ip daddr 1.0.0.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "amn0*" ip daddr 127.0.0.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "amn0*" ip daddr 127.0.0.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "tun0*" ip daddr 127.0.0.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "tun0*" ip daddr 127.0.0.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "tun2*" ip daddr 127.0.0.1 udp dport 53 counter packets 0 bytes 0 accept
oifname "tun2*" ip daddr 127.0.0.1 tcp dport 53 counter packets 0 bytes 0 accept
oifname "amn0*" ip daddr 127.0.0.53 udp dport 53 counter packets 0 bytes 0 accept
oifname "amn0*" ip daddr 127.0.0.53 tcp dport 53 counter packets 0 bytes 0 accept
oifname "tun0*" ip daddr 127.0.0.53 udp dport 53 counter packets 0 bytes 0 accept
oifname "tun0*" ip daddr 127.0.0.53 tcp dport 53 counter packets 0 bytes 0 accept
oifname "tun2*" ip daddr 127.0.0.53 udp dport 53 counter packets 0 bytes 0 accept
oifname "tun2*" ip daddr 127.0.0.53 tcp dport 53 counter packets 0 bytes 0 accept
}
chain amnvpn.a.310.blockDNS {
counter packets 100 bytes 6624 jump amnvpn.310.blockDNS
}
chain amnvpn.310.blockDNS {
udp dport 53 counter packets 100 bytes 6624 reject
tcp dport 53 counter packets 0 bytes 0 reject
}
chain amnvpn.a.300.allowLAN {
counter packets 0 bytes 0 jump amnvpn.300.allowLAN
}
chain amnvpn.300.allowLAN {
ip daddr 10.0.0.0/8 counter packets 0 bytes 0 accept
ip daddr 169.254.0.0/16 counter packets 0 bytes 0 accept
ip daddr 172.16.0.0/12 counter packets 0 bytes 0 accept
ip daddr 192.168.0.0/16 counter packets 0 bytes 0 accept
ip daddr 224.0.0.0/4 counter packets 0 bytes 0 accept
ip daddr 255.255.255.255 counter packets 0 bytes 0 accept
}
chain amnvpn.a.290.allowDHCP {
counter packets 0 bytes 0 jump amnvpn.290.allowDHCP
}
chain amnvpn.290.allowDHCP {
ip daddr 255.255.255.255 udp sport 68 udp dport 67 counter packets 0 bytes 0 accept
}
chain amnvpn.a.200.allowVPN {
counter packets 0 bytes 0 jump amnvpn.200.allowVPN
}
chain amnvpn.200.allowVPN {
oifname "amn0*" counter packets 0 bytes 0 accept
oifname "tun0*" counter packets 0 bytes 0 accept
oifname "tun2*" counter packets 0 bytes 0 accept
}
chain amnvpn.a.120.blockNets {
counter packets 0 bytes 0 jump amnvpn.120.blockNets
}
chain amnvpn.120.blockNets {
}
chain amnvpn.a.110.allowNets {
counter packets 0 bytes 0 jump amnvpn.110.allowNets
}
chain amnvpn.110.allowNets {
ip daddr [VPN's IP] counter packets 0 bytes 0 accept
}
chain amnvpn.a.100.blockAll {
counter packets 0 bytes 0 jump amnvpn.100.blockAll
}
chain amnvpn.100.blockAll {
counter packets 0 bytes 0 reject
}
chain OUTPUT {
type filter hook output priority filter; policy accept;
counter packets 204 bytes 16232 jump amnvpn.anchors
}
}
# Warning: table ip6 filter is managed by iptables-nft, do not touch!
table ip6 filter {
chain amnvpn.anchors {
counter packets 9 bytes 576 jump amnvpn.a.000.allowLoopback
counter packets 9 bytes 576 jump amnvpn.a.310.blockDNS
counter packets 9 bytes 576 jump amnvpn.a.300.allowLAN
counter packets 9 bytes 576 jump amnvpn.a.290.allowDHCP
counter packets 9 bytes 576 jump amnvpn.a.250.blockIPv6
counter packets 9 bytes 576 jump amnvpn.a.200.allowVPN
counter packets 9 bytes 576 jump amnvpn.a.100.blockAll
}
chain amnvpn.a.000.allowLoopback {
counter packets 0 bytes 0 jump amnvpn.000.allowLoopback
}
chain amnvpn.000.allowLoopback {
oifname "lo*" counter packets 0 bytes 0 accept
}
chain amnvpn.a.310.blockDNS {
}
chain amnvpn.310.blockDNS {
udp dport 53 counter packets 0 bytes 0 reject
tcp dport 53 counter packets 0 bytes 0 reject
}
chain amnvpn.a.300.allowLAN {
counter packets 0 bytes 0 jump amnvpn.300.allowLAN
}
chain amnvpn.300.allowLAN {
ip6 daddr fc00::/7 counter packets 0 bytes 0 accept
ip6 daddr fe80::/10 counter packets 0 bytes 0 accept
ip6 daddr ff00::/8 counter packets 0 bytes 0 accept
}
chain amnvpn.a.290.allowDHCP {
counter packets 0 bytes 0 jump amnvpn.290.allowDHCP
}
chain amnvpn.290.allowDHCP {
ip6 daddr ff00::/8 udp sport 546 udp dport 547 counter packets 0 bytes 0 accept
}
chain amnvpn.a.250.blockIPv6 {
counter packets 0 bytes 0 jump amnvpn.250.blockIPv6
}
chain amnvpn.250.blockIPv6 {
oifname != "lo*" counter packets 0 bytes 0 reject
}
chain amnvpn.a.200.allowVPN {
}
chain amnvpn.200.allowVPN {
oifname "amn0*" counter packets 0 bytes 0 accept
oifname "tun0*" counter packets 0 bytes 0 accept
oifname "tun2*" counter packets 0 bytes 0 accept
}
chain amnvpn.a.100.blockAll {
counter packets 0 bytes 0 jump amnvpn.100.blockAll
}
chain amnvpn.100.blockAll {
counter packets 0 bytes 0 reject
}
chain OUTPUT {
type filter hook output priority filter; policy accept;
counter packets 9 bytes 576 jump amnvpn.anchors
}
}
table ip raw {
chain amnvpn.anchors {
counter packets 104 bytes 9608 jump amnvpn.a.100.vpnTunOnly
}
chain amnvpn.a.100.vpnTunOnly {
}
chain amnvpn.100.vpnTunOnly {
counter packets 0 bytes 0 accept
}
chain PREROUTING {
type filter hook prerouting priority raw; policy accept;
counter packets 104 bytes 9608 jump amnvpn.anchors
}
}
table ip6 raw {
chain amnvpn.anchors {
counter packets 5 bytes 320 jump amnvpn.a.100.vpnTunOnly
}
chain amnvpn.a.100.vpnTunOnly {
}
chain amnvpn.100.vpnTunOnly {
counter packets 0 bytes 0 accept
}
chain PREROUTING {
type filter hook prerouting priority raw; policy accept;
counter packets 5 bytes 320 jump amnvpn.anchors
}
}
# Warning: table ip nat is managed by iptables-nft, do not touch!
table ip nat {
chain amnvpn.anchors {
counter packets 2 bytes 104 jump amnvpn.a.100.transIp
}
chain amnvpn.a.100.transIp {
}
chain amnvpn.100.transIp {
counter packets 0 bytes 0 masquerade
}
chain POSTROUTING {
type nat hook postrouting priority srcnat; policy accept;
counter packets 2 bytes 104 jump amnvpn.anchors
}
}
# Warning: table ip6 nat is managed by iptables-nft, do not touch!
table ip6 nat {
chain amnvpn.anchors {
counter packets 2 bytes 144 jump amnvpn.a.100.transIp
}
chain amnvpn.a.100.transIp {
}
chain amnvpn.100.transIp {
counter packets 0 bytes 0 XT target MASQUERADE not found
}
chain POSTROUTING {
type nat hook postrouting priority srcnat; policy accept;
counter packets 2 bytes 144 jump amnvpn.anchors
}
}
# Warning: table ip mangle is managed by iptables-nft, do not touch!
table ip mangle {
chain amnvpn.anchors {
counter packets 204 bytes 16232 jump amnvpn.a.100.tagPkts
}
chain amnvpn.a.100.tagPkts {
}
chain amnvpn.100.tagPkts {
meta cgroup 1383 counter packets 0 bytes 0 meta mark set 0x3211
}
chain OUTPUT {
type route hook output priority mangle; policy accept;
counter packets 204 bytes 16232 jump amnvpn.anchors
}
}
# Warning: table ip6 mangle is managed by iptables-nft, do not touch!
table ip6 mangle {
chain amnvpn.anchors {
counter packets 9 bytes 576 jump amnvpn.a.100.tagPkts
}
chain amnvpn.a.100.tagPkts {
}
chain amnvpn.100.tagPkts {
meta cgroup 1383 counter packets 0 bytes 0 meta mark set 0x3211
}
chain OUTPUT {
type route hook output priority mangle; policy accept;
counter packets 9 bytes 576 jump amnvpn.anchors
}
}