Testing Qubes OS is not an easy task. It’s not like you can run Qubes on the browser… or can you?!
That’s what we’re about to find out…
What you’ll need
- a random test laptop running Qubes 4.1
- internet connection
A word of caution
This setup involves completely invalidating the security properties of your Qubes installation. Do this only on a device used exclusively for testing.
Additionally, participants will have access to the device as though they were next to you. If you connect the device to you home’s WiFi, you should consider the risk of them being able to see its password or even find your home’s physical address by your home network’s name or the ones around.
Overview
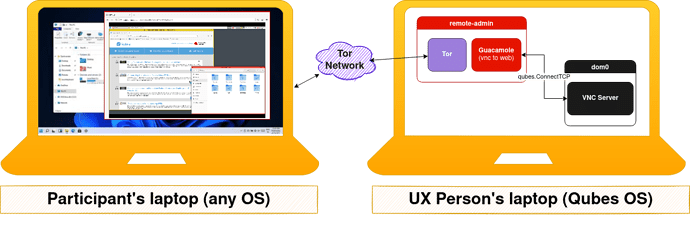
We have two devices: the participant’s, which just needs to run Tor Browser and the UX Person’s, which is running Qubes.
Limitations
- 2-20 seconds input delay - can be improved if you use DNS instead of onion services. It really depends on your Tor circuit. I have been able to use with 2-4 seconds.
1. Create qube: remote-admin
Create a new qube called remote-admin with the following settings:
| Type | StandaloneVM |
| Template | debian-11 ( |
Advanced: for simplicity of software installation and persistence we create a standalone qube. Advanced users can probably figure out how to do the same with templates and app qubes.
2. Install remote screen sharing software in dom0:
instructions borrow from here (in case they break check there).
Run the following in a dom0 terminal:
# install the qubes contributor's repository
sudo qubes-dom0-update qubes-repo-contrib
# install the remote-desktop software
sudo qubes-dom0-update qubes-remote-desktop
# set "VNCPASS" as the password
vncpasswd
#enable the qubes-x0vncserver (for some reason)
qvm-service --enable dom0 qubes-x0vncserver
![]() and then start the dom0 VNC service
and then start the dom0 VNC service
systemctl start qubes-x0vncserver@$(whoami)
2. Configure policy dom0 ↔ remote-admin
In dom0’s terminal type the following:
echo "qubes.ConnectTCP +5900 remote-admin @default allow target=dom0" | sudo tee /etc/qubes/policy.d/30-remote-admin.policy
3. (optional) Check that you have dom0 access from remote-admin
In remote-admin:
 open a terminal and run
open a terminal and run qvm-connect-tcp 5900:@default:5900
Good point to test
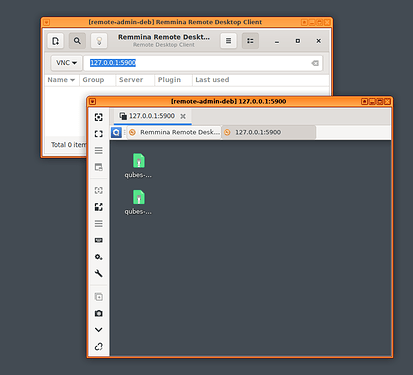
At this stage you can check if you are correctly getting. You can install a VNC viewer likeremminaand connect to127.0.0.1:5900. Then it will ask the passwordVNCPASS(you set it earlier).
Troubleshooting
- vnc connection failure: too many security failures
Just restart the vnc server in dom0systemctl restart qubes-x0vncserver@$(whoami)
4. Install the guacamole server (vnc to web)
Guacamole essentially allows users to connect via their web browser to a VNC server.
Still in the remote-admin qube
- You install it like this:
sudo apt install -y guacd libguac-client-vnc0
sudo apt install -y tomcat9 tomcat9-admin tomcat9-common tomcat9-user
-
Download the latest guacamole
.warfrom Apache Guacamole™: Release Archive -
Verify the file integrity with the
sha256hashes on the website
(can save you some troubleshooting time in case your download breaks) -
Copy the downloaded file onto
/var/lib/tomcat9/webapps/guacamole.war(may need sudo) -
restart tomcat for the newly installed
.war
sudo systemctl restart tomcat9 -
Edit the file
/etc/guacamole/user-mapping.xml(you may need to create/etc/guacamole/)
<user-mapping>
<authorize username="user" password="pass">
<protocol>vnc</protocol>
<param name="hostname">127.0.0.1</param>
<param name="port">5900</param>
<param name="password">123456</param>
</authorize>
</user-mapping>
-
Restart guacamole to apply the changes:
sudo systemctl restart guacd. -
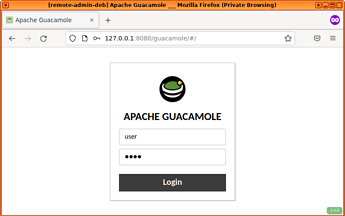
Open firefox on the webpage:
http://127.0.0.1:8080/guacamole.You should see a login page. Your credentials are:
user: user
pass: pass
Hurray!
Now you have a functioning dom0 remote access via the web browser.But this is not super useful since it is just local access and you can’t give that address for a user to test. In the next section, we’ll show you how you can generate an address where your users can test your system.
4. Create a .onion address for it
sudo apt install tor- edit the file
/etc/tor/torrcand add the following text at the end and save it:
HiddenServiceDir /var/lib/tor/guacamole_vnc
HiddenServicePort 80 127.0.0.1:8080
HiddenServiceVersion 3
-
restart Tor to apply the changes
sudo systemctl restart tor -
Obtain your
.onionaddress
sudo cat /var/lib/tor/guacamole_vnc/hostname Save this link as that will be what you share with your participants.
Save this link as that will be what you share with your participants.
Just be aware that they have to install the Tor Browser in order to access it. -
Grab some tea
 while the onion address propagates through the Tor network. (max 10 mins)
while the onion address propagates through the Tor network. (max 10 mins)
5. Share the link with your participants
- Send
yoursite.onion/guacamolewith participants - Tell them to log in with:
user: user
pass: pass
When you restart your computer
Everything with ![]() you have to run every time you restart your computer / remote-admin qube.
you have to run every time you restart your computer / remote-admin qube.
Tips & Tricks
 Hiding
Hiding remote-admin qube
Because an extra qube is running it could interfere with a user’s experience (e.g. they will see it in the qube domains widget). To hide it, you can delete sys-whonix or sys-usb and rename remote-admin to either one. An unsuspecting users won’t see any difference.
Making this faster
See this related discussions.
Credits
-
@fepitre for putting together qubes-remote-desktop and pointing me to it
-
Inspiration from this guide and this discussion.
-
byzanz developers, which made a tool that can be installed in dom0 through the repos and allows for creating gifs from dom0.
 Xzibit style
Xzibit style