Using a YubiKey can help protect your system from an attack that knows your LUKS password. The YubiKey Challenge-Response authentication doesn’t use a time component, if the attacker has access to both the key and your password they will be able to extract the permanent LUKS password.
Make sure you have a full backup of your system before you try to modify your LUKS authentication, if you mess something up, there might be no way to recover without a backup.
I will be using Debian 12, the yubikey-personalization installation might be different on Fedora, but setting up the key should be the same for both distributions.
You are going to be generating an LUKS key, you might want to do that step offline in a disposable qube, just to be sure it’s not possible to recover the key when you are done.
The following steps are done is an appvm
Clone repositories
$ git clone https://github.com/the2nd/ykluks
This repository has the code needed to use the YubiKey at the LUKS prompt
$ git clone https://github.com/Yubico/yubikey-personalization.git
This is needed one time to set up the key
Install dependencies
You don’t need to add the packages to a template, you only need to use them once.
$ sudo apt install libyubikey-dev dh-autoreconf libusb-dev asciidoc xsltproc make
Compile yubikey-personalization
cd yubikey-personalization
autoreconf --install
./configure
make
Setup key and password
Insert the YubiKey and attach the USB device to the qube with yubikey-personalization.
This will configure slot 2 of the YubiKey for the challenge response, make sure it’s not conflicting with how you use your key.
$ sudo ./ykpersonalize -2 -ochal-resp -ochal-hmac -ohmac-lt64 -oserial-api-visible
$ sudo ./ykchalresp -2 <YOUPASSWORD>
The output from ykchalresp will later be used as the new LUKS password, make sure you keep a secure copy. YOURPASSWORD is the password you use at the password prompt.
Make a tar archive of the ykluks repository
$ tar czf ykluks.tar.gz ykluks
The following steps are done in dom0
Install ykpers
$ sudo qubes-dom0-update ykpers
Find a free key slot, normally only slot 0 will be in use.
$ sudo cryptsetup luksDump /dev/nvme0n1p3
Add the ykluks key to keyslot 1
$ sudo cryptsetup luksAddKey --key-slot 1 /dev/nvme0n1p3
The key you add is the output ykchalresp.
Copy ykluks to dom0 and install
qvm-run --pass-io <VM-NAME> 'cat ~/ykluks.tar.gz' > ykluks.tar.gz
tar xf ykluks.tar.gz
cd ykluks
sudo ./install
Edit /etc/default/grub
Changed the lines:
rd.luks.uuid=luks-...
rd.qubes.hide_all_usb
To:
rd.ykluks.uuid=luks-...
rd.ykluks.hide_all_usb
Update grub and dracut
sudo grub2-mkconfig -o /boot/grub2/grub.cfg
sudo dracut -f
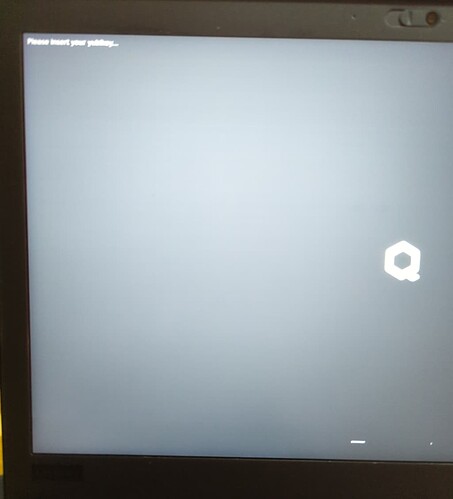
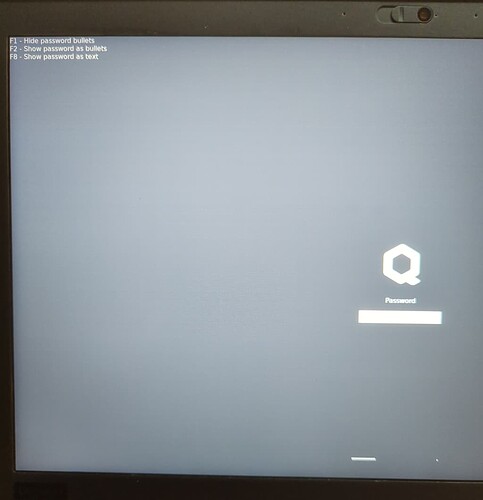
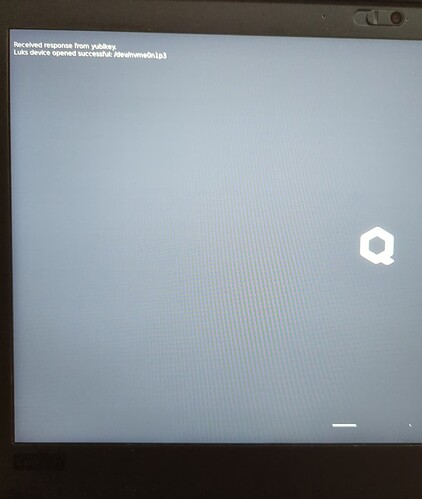
Reboot and test if the key is working.
At the LUKS password prompt use ESC to get to the text console, both the normal LUKS prompt and the ykluks prompt will be asking for your password. Just type the ykluks password in all prompts and the system should eventually unlock. If the ykluks password doesn’t work, you should still be able to use your normal LUKS password.
You should now be able to unlock LUKS using the YubiKey and password, do not proceed if there are any issues using the key
Remove the old password in keyslot 0
$ sudo cryptsetup luksKillSlot /dev/nvme0n1p3 0
Disable the standard LUKS password prompt.
There might be a better way of doing this, but this worked for me.
cd /usr/lib/dracut/modules.d
sudo mv 90crypt x90crypt
sudo dracut -f
This should make it so there is only one password prompt when you unlock LUKS.
If you ever need to access the system without the YubiKey, you can boot into the emergency shell and unlock LUKS using the output from ykchalresp. From there you should be able to restore 90crypt, and add a new password with cryptsetup.