Lately I’ve been tinkering around trying to get full desktop environment out of Debian and Fedora xfce templates. More specifically, I am curious to know what exactly prevents them from showing me their beautiful whiskers. I also want to do it without uninstalling stuff, just a reconfiguration, as minimal as possible, preferably easily reversible. Here’s what I come up with:
#!/usr/bin/env bash
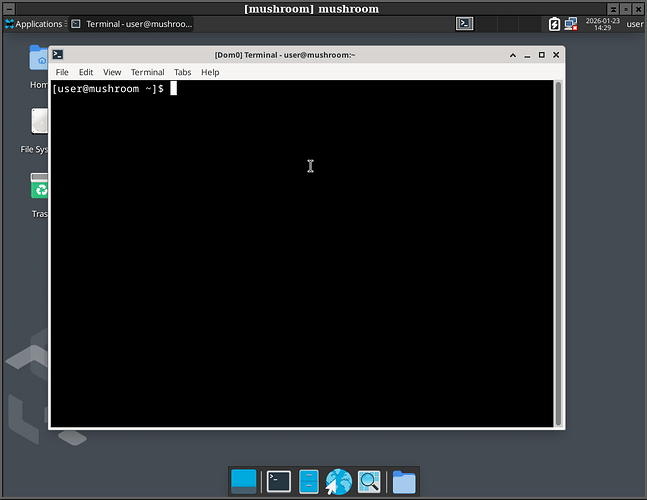
qvm-clone fedora-42-xfce mushroom
# run `systemctl set-default multi-user.target` to revert this
qvm-run -u root mushroom -- systemctl set-default graphical.target
# Fedora login screen won't let you through without a password, and auto-login doesn't work for some reason.
qvm-run -u root mushroom -- 'echo "user" | passwd --stdin user'
qvm-prefs mushroom debug true
qvm-prefs mushroom virt_mode hvm
qvm-prefs mushroom kernel ''
qvm-prefs mushroom memory 1000
qvm-prefs mushroom maxmem 0
qvm-service mushroom lightdm on
qvm-shutdown mushroom
#!/usr/bin/env bash
qvm-clone debian-13-xfce plank
qvm-run -u root plank -- mv /etc/X11/xorg-qubes.conf /etc/X11/xorg-qubes.conf.backup
qvm-prefs plank debug true
qvm-prefs plank virt_mode hvm
qvm-prefs plank kernelopts "systemd.unit=graphical.target" # thanks ddevz!
qvm-service plank lightdm on
qvm-shutdown plank
I don’t like two things about this. First, both cases require setting virt_mode to hvm - otherwise you won’t get the window upon starting your vm. It would be nice to have a full-desktop pvh. Second, fedora boots and works with qubes kernel but won’t start desktop environment (or at least it doesn’t display it), which forces me to use distribution kernel and disable memory balancing. Not cool.
Perhaps most interesting discovery is the lightdm service. From qvm-service manual:
lightdm:
Default: disabled
Start lightdm and avoid starting qubes-gui-agent. In this case,
lightdm is responsible to start the X.org server.
Mainly because nobody seems to be aware of it on this forum, at least not in the related topics I have checked. It also doesn’t do everything that manual says - it doesn’t result in working xorg. You still need to set graphical target.
It would be nice to see full desktop VMs as first citizens in qubes. Without the jank of unresizeable window, at least. Right now we’re mildly stuck with the templates we have.
Why am I doing this?
For fun, I guess. Speaking of fun: if you get full desktop in a template, windows there are marked as dom0’s: