I’m just a dumb civilian, and have never been anything else, but those who know what to look for on LinkedIn would see the traces of retired CIA, DIA, SOCOM, etc. A little bit of my work ended up in a Joint Special Operations University class years ago, I sometimes have interactions with National Defense University authors. I quite pointedly do NOT get along with the trolls with badges that make up DHS and FBI. So … not anti-authority, but I have a real problem with what corrupts authority.
With that background I will say that I wrote the white paper that led to twenty House offices calling for hearings on HBGary. During those years various parts of the DoD were seeking “persona management” systems and misattrib/no attrib system vendor Ntrepid’s name was mentioned. As what I do evolves, I meet new people, including the company’s founder a few years ago. The cost for a single seat of Windows with them running all the hardware/software/network was around $10k/month. I did a little work with a potential competitor, didn’t care for the people I encountered, and that’s long since gone over my event horizon.
The people who can employ something like Qubes are “operators”, that’s shorthand for resourceful, multitalented folks - hackers, journalists, human rights activists, people whose drivers are internal. The only way they stop is if someone makes them stop.
The large hierarchies get people who can do the sort of human factors/influence ops stuff I write about, but they won’t have the breadth to do their own technology, nor would they get trained to do so. It’s just too complex, too demanding, hence the $10k/seat mistattrib systems for those who can NOT get caught slipping.
So I get along with the spooks, I know a bit about the norms and economics in that world, but my daily grind is civil society orgs and their support, those multitalented folks who just can’t keep out of trouble  It’s normal to see groups working with their one cell phone and one laptop. A portion of them can be encouraged to keep older gear and repurpose it for safety’s sake. A smaller percentage will do things like what I do - compartmentalization and the human and hardware level.
It’s normal to see groups working with their one cell phone and one laptop. A portion of them can be encouraged to keep older gear and repurpose it for safety’s sake. A smaller percentage will do things like what I do - compartmentalization and the human and hardware level.
As I look at Russia/Ukraine, China/Taiwan, Israel/Gaza, Colombia/Guyana, this all reminds me of the 1930s. It hasn’t really started yet, but it’s going to, there’s no way to pull back from it now. I’m on the side of the humans in this, I’m much closer to the end of my career than the start, so much so that I’m spending more time trying to keep folks from learning the hard way than I am actually doing anything on my own any more.
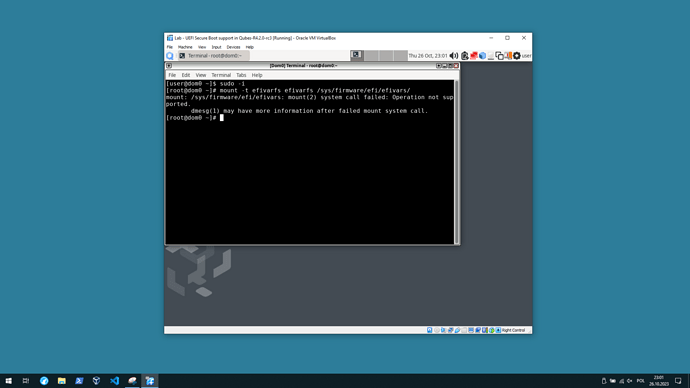
And that’s why I want to virtualize, just aiming for an economy of motion on my part, I don’t imagine anyone is going to try that in anything other than a lab environment. So I don’t need a fancy book, just some general boundaries so I don’t waste hours on end going down rabbit holes.