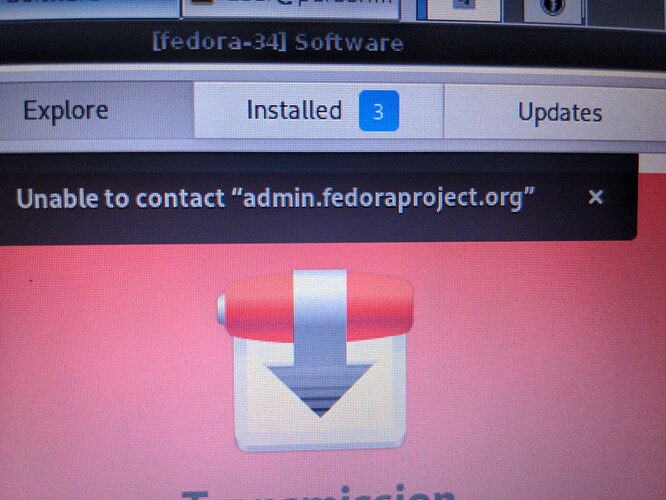
I want to install apps on the Fedora33 or 34 template. When opening the preinstalled GNOME Software I receive the error message “Unable to contact admin.fedoraproject.org”. I can browse the shop and the sites are loaded, though pretty slow. But when clicking install there is no installation progress for the apps (Status endless “in Progress”).
@GMueller Sadly, I don’t think I have ever been able to make the software GUI work properly. You will have a much easier time in the long run installing and updating software using the terminal within each template.
I know you are new to both Linux and Qubes (from your comments on another thread), so you are probably cringing… but this issue aside, there is no way around the terminal if you are going to be using Qubes.
I also began using Qubes with no Linux experience. The sooner you make friends with the command line, the better. There are many other things you will regularly need to do in a terminal to keep your Qubes system operating smoothly (i.e. no GUI options). Package installations and updates are a good way to get started. It’s where most people begin.
For now, browse the GUI software interface and make a list of the apps you want to install. Then do a quick web search for “app name + Fedora install” (For what it’s worth, I personally prefer Debian templates whenever possible). Sometimes it’s a simple one-liner sudo dnf install vlc other times its a few commands. But initially, it’s just a matter of copying from a trusted source and pasting it into your terminal. It’s tedious but easy. It becomes less tedious with time.
Pro tip: Ideally type the commands manually and carefully proof read them. At the very least, copy and paste commands from a web page into a plain text editor first, then copy from the text editor and paste into the terminal. that will help prevent hidden text (which is very easy to hide in a web page) from executing in your terminal.
I hope this isn’t discouraging… just typing this message makes it seem like a big hassle but it’s really not. Once you get familiar certain commands, they are very fast and simple to use. In time, you will certainly prefer certain commands over GUI.
Hello my friend @necker , thank you very much for your feedback! Of course, though I may want to hear something else (like “GUI sufficient to work out anything”  ), this is very helpful. Also thanks for the hints regards copying text from the web! I am getting more and more familiar with “linux” and terminal commands. But there is a lot to learn ahead for sure
), this is very helpful. Also thanks for the hints regards copying text from the web! I am getting more and more familiar with “linux” and terminal commands. But there is a lot to learn ahead for sure  privacy is worth it.
privacy is worth it.
I am tending to Debian as well. But I was trying Fedora since it seems to have a stronger relation to Qubes by installation, at least to my perception.
Yes, dom0 is Fedora and default templates are also Fedora, however, there is an option to choose Debian for the default templates when installing Qubes. I personally prefer that. You might try that next time you install Qubes. In the mean time, get to know Fedora. dom0 is always Fedora so it’s good to know.
Just figured out accidentally when starting Fedora TemplateVM Updates / Installation the SYS-WHONIX template starts? I am not using Network, how can I change settings for updates / package installation? I assume using TOR may cause issues when using Software app or making installations. Am a bit confused
The package manager in each template uses an update proxy via port 8082 instead of standard network access.
When “update” is chosen in Qubes Manager, the template will start and access the internet through the Qubes Update Proxy via the dom0 update qube that you specify (see Qubes Manager → system → Global Settings → qube defaults) . Given your description, you likely selected “updates over Tor” when installing Qubes, so your dom0 update qube is sys-whonix. That’s why sys-whonix is starting. That is how your templates can access online packages with no NetVM. That’s okay.
No comment on the Software app. 
I assume you mean the sys-whonix qube - not a template.
This is most likely because you selected to run updates over Tor at
installation.
Depending on which Qubes version you are running, you can check this in
different places, and change the method.
In 4.0 edit the file /etc/qubes-rpc/policy/qubes.UpdatesProxy: you
want templates to point to sys-firewall, not sys-whonix. (I don’t have a
4.0 to hand but I think you can do this by commenting the line that
refers to target=sys-whonix - make sure you check this.
In 4.1 check that file AND /etc/qubes/policy.d/90-default.policy
The built in Fedora GUI software tool does not work well with the proxy method
that Qubes uses, as said. It’s confused by the absence of a network
connection.
Running updates and installs over Tor does not cause issues - it may run
more slowly depending on your network connection, but other than that
will be fine.
In Debian there is an excellent tool called aptitude which you can
run in a terminal and will allow you to search software packages, and
install. Debian does play nicely with offline templates.
Give it a try.
When I comment in the Forum or in the mailing lists I speak for myself.
Indeed I installed Qube using TOR for updates but changed UpdateVM in the global settings from whonix to sys-firewall. It seems that this is not enough and I need to change proxy settings
Thanks will check! Found to use Synaptic for Package Managing on Debian and be quite happy with it. dnfdragora as GUI for Fedora seems ok too
Using R4.0
/etc/qubes-rpc/policy/qubes.UpdatesProxy → Changed the following (bold) “sys-whonix” entry to “sys-firewall” and it seemed to work first, but then received proxy error message when trying to install something on Fedora TemplateVM. Which entries do you recommend to amend?
$type:TemplateVM $default allow,target=sys-whonix
Note that policy parsing stops at the first match,
so adding anything below “$anyvm $anyvm action” line will have no effectPlease use a single # to start your custom comments
Upgrade all TemplateVMs through sys-whonix.
$type:TemplateVM $default allow, target=sys-whonix → sys-firewall
Upgrade Whonix TemplateVMs through sys-whonix.
$tag:whonix-updatevm $default allow,target=sys-whonix
Deny Whonix TemplateVMs using UpdatesProxy of any other VM.
$tag:whonix-updatevm $anyvm deny
Default rule for all TemplateVMs - direct the connection to sys-net
$type:TemplateVM $default allow,target=sys-net
$anyvm $anyvm deny
This seems to help (put # in front of 1st line): https://www.reddit.com/r/Qubes/comments/92xtqr/how_do_i_change_my_update_qube/
Curiously, why do you want to change from sys-whonix to sys-firewall? There is nothing wrong with updating over Tor. Many people do that and find it to be a more secure/anonymous option.
When configuring qubes.UpdatesProxy, I believe you need to change all instances of sys-whonix to sys-firewall (if that is your preference). In your above example, you only seem to have modified one of the lines.
That was my intention initially to use TOR but I had the impression that using it for updating may cause issues and may not be preferable anytime. Once I had problem with updating FEDORA I read that somewhere that TOR may be the reason. Thanks to you guys I know now where to make amendments to “play around” and test it the one way or the other.
When I replaced all sys-whonix entries with sys-firewall I received complex error messages when trying to install packages on TemplateVMs, so I amended further. Finally only the # infront of first line helped me to connect via sys-firewall