This guide was created for simplicity, because the official guide on the Kicksecure page isn’t always clear to newcomers using Qubes, and some commands for the Debian template differ from those for native Debian.
Many users don’t want to install additional templates and just want to harden Debian template. Some users find lxqt‑tools inconvenient.
So we will install the CLI-version. It will also install significantly fewer packages in the Debian template.
Comment of Kicksecure team about CLI-version:
Command line interface (CLI) version only. This does not modify the graphical desktop environment. This package provides better kernel hardening, improved entropy, and other security features.
Update tempale, open terminal in debian-13 or debian-13-xfce and enter this commands:
sudo apt install --no-install-recommends adduser
sudo /usr/sbin/adduser user sudo
Reboot template and run terminal again
sudo /usr/sbin/addgroup --system console
sudo /usr/sbin/adduser user console
sudo apt install console-data console-common kbd keyboard-configuration
sudoedit /etc/extrepo/config.yaml
Paste at the end (or delete # at the end)
- contrib
- non-free
Press Ctrl + O to save file.
Press Ctrl + X to exit nano editor.
sudo http_proxy=http://127.0.0.1:8082 https_proxy=http://127.0.0.1:8082 extrepo enable kicksecure
sudo apt update
sudo apt install --no-install-recommends kicksecure-qubes-server
Enter “Don't touch keymap” on Configuring console-data window, then Ok
sudo apt install --no-install-recommends mokutil tirdad
sudo repository-dist --enable --repository stable
sudo extrepo disable kicksecure
sudo mv /etc/apt/sources.list ~/
sudo touch /etc/apt/sources.list
sudo /usr/sbin/adduser user privleap
Done
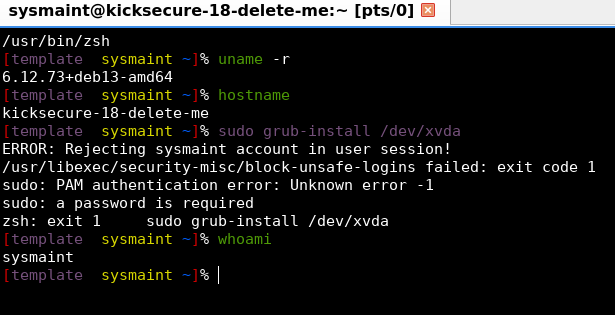
If you want to install sysmaint for hardening and high security, run this command:
sudo apt install --no-install-recommends user-sysmaint-split sysmaint-panel
Done
![]() Now your Debian template and any AppVMs built from it have strong protection!
Now your Debian template and any AppVMs built from it have strong protection!
For extra security, you can add AppArmor profiles to the Debian template:
Apparmor profile for Qubes available!
Also, you can run amnesic RAM-base Debian appVMs to protect against forensics:
dom0 in RAM (zram0, overlay in tmpfs)
Really disposable (RAM based) qubes