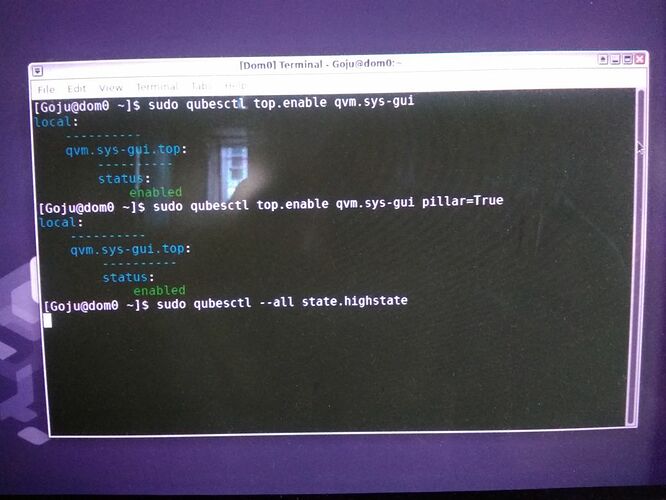
I got error code 1. Please find the output of dom0 terminal.
[Anirban@dom0 ~]$ sudo qubesctl top.enable qvm.sys-gui
local:
----------
qvm.sys-gui.top:
----------
status:
enabled
[Anirban@dom0 ~]$ sudo qubesctl top.enable qvm.sys-gui pillar=True
local:
----------
qvm.sys-gui.top:
----------
status:
enabled
[Anirban@dom0 ~]$ sudo qubesctl --all state.highstate
[ERROR ] Command ‘systemd-run’ failed with return code: 1
[ERROR ] stdout: Running scope as unit: run-rc28f9fd9937b4a92af56de82f7460ead.scope
Using sys-firewall as UpdateVM to download updates for Dom0; this may take some time…
Running ‘/usr/lib/qubes/qubes-download-dom0-updates.sh --doit --nogui ‘–exclude=qubes-template-whonix-gw-15,qubes-template-debian-10,qubes-template-fedora-34,qubes-template-whonix-ws-15’ ‘-y’ ‘–best’ ‘–allowerasing’ ‘–clean’ ‘–action=install’ ‘qubes-template-fedora-34-xfce’’ on sys-firewall
sys-firewall: command failed with code: 1
[ERROR ] retcode: 1
[ERROR ] Error occurred installing package(s). Additional info follows:
errors:
- Running scope as unit: run-rc28f9fd9937b4a92af56de82f7460ead.scope
Using sys-firewall as UpdateVM to download updates for Dom0; this may take some time…
Running ‘/usr/lib/qubes/qubes-download-dom0-updates.sh --doit --nogui ‘–exclude=qubes-template-whonix-gw-15,qubes-template-debian-10,qubes-template-fedora-34,qubes-template-whonix-ws-15’ ‘-y’ ‘–best’ ‘–allowerasing’ ‘–clean’ ‘–action=install’ ‘qubes-template-fedora-34-xfce’’ on sys-firewall
sys-firewall: command failed with code: 1
[ERROR ] ====== [‘present’] ======
====== stderr ======
/usr/bin/qvm-create sys-gui --class=AppVM --template=fedora-34-xfce --label=black
app: Error creating VM: Got empty response from qubesd. See journalctl in dom0 for details.
====== [‘prefs’] ======
Virtual Machine does not exist!
====== [‘service’] ======
[SKIP] Skipping due to previous failure!
====== [‘features’] ======
[SKIP] Skipping due to previous failure!
local:
ID: topd-always-passes
Function: test.succeed_without_changes
Name: foo
Result: True
Comment: Success!
Started: 20:01:57.951700
Duration: 0.984 ms
Changes:
ID: qubes-template-fedora-34-xfce
Function: pkg.installed
Result: False
Comment: Error occurred installing package(s). Additional info follows:
errors:
- Running scope as unit: run-rc28f9fd9937b4a92af56de82f7460ead.scope
Using sys-firewall as UpdateVM to download updates for Dom0; this may take some time...
Running '/usr/lib/qubes/qubes-download-dom0-updates.sh --doit --nogui '--exclude=qubes-template-whonix-gw-15,qubes-template-debian-10,qubes-template-fedora-34,qubes-template-whonix-ws-15' '-y' '--best' '--allowerasing' '--clean' '--action=install' 'qubes-template-fedora-34-xfce'' on sys-firewall
sys-firewall: command failed with code: 1
Started: 20:02:02.712592
Duration: 292687.428 ms
Changes:
ID: dummy-psu-sender
Function: pkg.installed
Result: True
Comment: The following packages were installed/updated: dummy-psu-sender
Started: 20:06:55.400359
Duration: 26406.807 ms
Changes:
----------
dummy-psu-sender:
----------
new:
1.0.0-2.fc32
old:
ID: dummy-backlight-dom0
Function: pkg.installed
Result: True
Comment: 1 targeted package was installed/updated.
Started: 20:07:21.849464
Duration: 24626.707 ms
Changes:
----------
dummy-backlight-dom0:
----------
new:
1.0.0-2
old:
ID: /usr/share/xsessions/sys-gui.desktop
Function: file.managed
Result: True
Comment: File /usr/share/xsessions/sys-gui.desktop updated
Started: 20:07:46.507336
Duration: 82.714 ms
Changes:
----------
diff:
New file
ID: sys-gui
Function: qvm.vm
Result: False
Comment: ====== ['present'] ======
====== stderr ======
/usr/bin/qvm-create sys-gui --class=AppVM --template=fedora-34-xfce --label=black
app: Error creating VM: Got empty response from qubesd. See journalctl in dom0 for details.
====== ['prefs'] ======
Virtual Machine does not exist!
====== ['service'] ======
[SKIP] Skipping due to previous failure!
====== ['features'] ======
[SKIP] Skipping due to previous failure!
Started: 20:07:46.603628
Duration: 818.917 ms
Changes:
ID: sys-gui-rpc
Function: file.managed
Name: /etc/qubes/policy.d/50-gui-sys-gui.policy
Result: True
Comment: File /etc/qubes/policy.d/50-gui-sys-gui.policy updated
Started: 20:07:47.422933
Duration: 21.854 ms
Changes:
----------
diff:
New file
ID: sys-gui-admin-local-rwx
Function: file.append
Name: /etc/qubes/policy.d/include/admin-local-rwx
Result: True
Comment: Appended 2 lines
Started: 20:07:47.445158
Duration: 21.312 ms
Changes:
----------
diff:
---
+++
@@ -8,3 +8,5 @@
## Add your entries here, make sure to append "target=dom0" to all allow/ask actions
+sys-gui @tag:guivm-sys-gui allow target=dom0
+sys-gui sys-gui allow target=dom0
ID: sys-gui-admin-global-rwx
Function: file.append
Name: /etc/qubes/policy.d/include/admin-global-rwx
Result: True
Comment: Appended 3 lines
Started: 20:07:47.466618
Duration: 3.329 ms
Changes:
----------
diff:
---
+++
@@ -8,3 +8,6 @@
## Add your entries here, make sure to append "target=dom0" to all allow/ask actions
+sys-gui @adminvm allow target=dom0
+sys-gui @tag:guivm-sys-gui allow target=dom0
+sys-gui sys-gui allow target=dom0
Summary for local
Succeeded: 7 (changed=6)
Failed: 2
Total states run: 9
Total run time: 344.670 s
DOM0 configuration failed, not continuing
[Anirban@dom0 ~]$